A common metaphor for the Internet is that it’s divided into neighborhoods. If your website is hosted on an IP address and using nameservers that allow or encourage criminal activity, then you’re in a “bad neighborhood”. Bad neighborhoods can exist because some hosting providers offer a space for criminals to set up domains to serve malicious content to visitors. Under these circumstances, the hosting providers turn a blind eye as long as they are making money. Another contributing factor that creates bad neighborhoods are compromised hosts used maliciously without the owners knowledge.
We’re going to take a walk through one of these bad neighborhoods in this blog post.
Enter at the Gate
Our introduction to this neighborhood began when we were alerted to network communications with a URL ending in ‘gate.php’. URLs ending in ‘gate.php’ are indicative of default C2 URL configurations for multiple botnet families; ZeuS, Andromeda, and Pony downloader.
Network communications:
http://exportproducts[.]se/axump/gate[.]php
![exportproducts[.]se/axump/ login panel](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31155239/export1-300x93.png)
Once we started to look at the infrastructure behind this, the nameservers stood out as suspicious. The nameservers are: ns1[.]steeldns[.]com and ns2[.]steeldns[.]com. A suspicious feature here is that the parent domain points to: localhost and 127.0.0.1.
![IP analysis of steeldns[.]com](https://cdn.umbrella.marketops.umbrella.com/wp-content/uploads/2018/02/25163817/85AA8956-B163-4260-B032-795C49D200D5-1024x215.png)
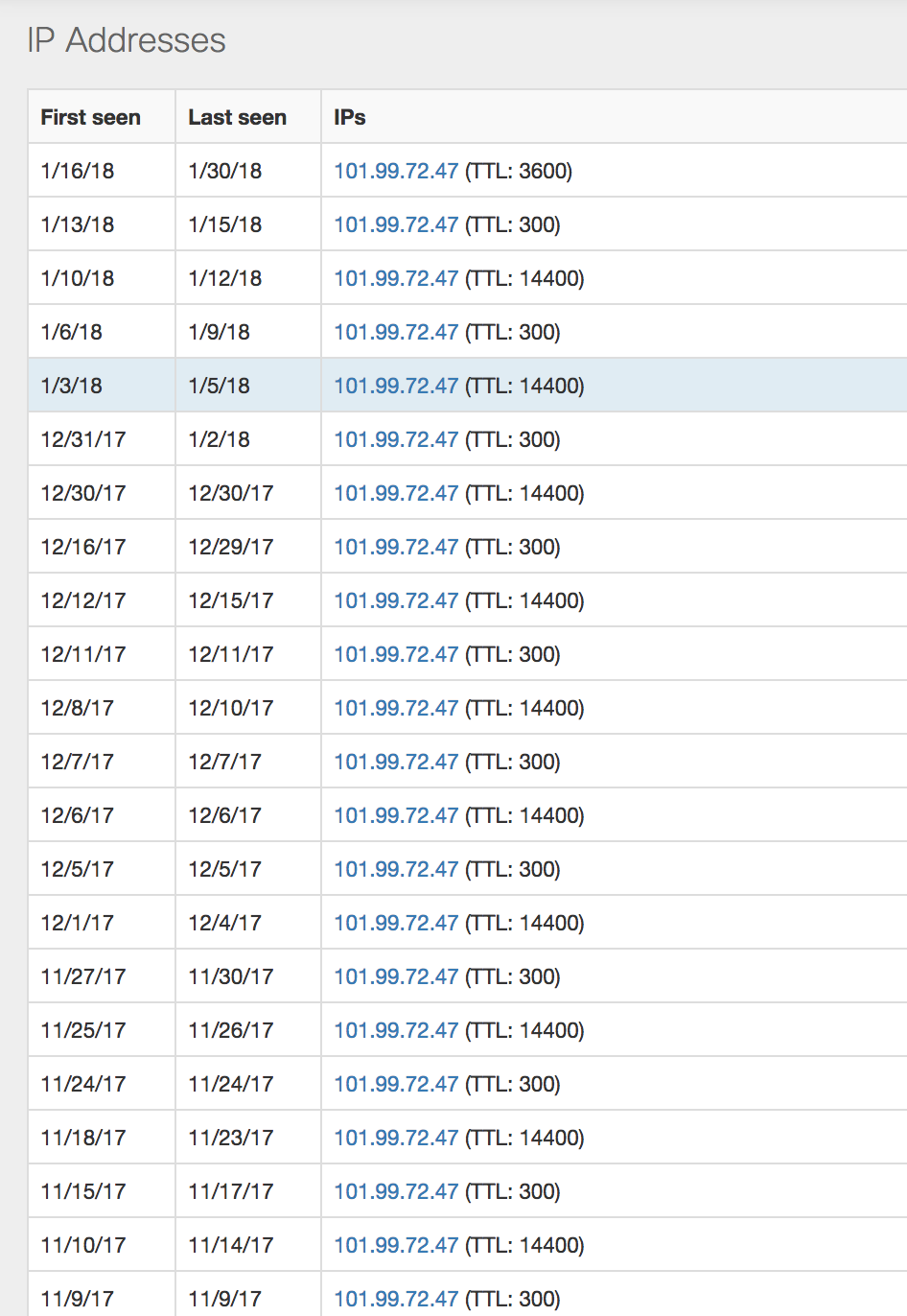
This particular host is consistently changing to a low TTL, but not changing the IP address. It doesn’t appear they’re successfully utilizing a Fast Flux technique, but it’s enough to appear suspicious.
A co-occurrence for ns1[.]steeldns[.]com is another nameserver ns2[.]metaldns[.]com. A co-occurrence is when two or more domains are being accessed by the same users within a small window of time. This top domain, metaldns[.]com is also pointed to localhost 127.0.0.1.
![Nameserver co-occurrence of ns1[.]steeldns[.]com](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31125000/co.png)
![IP analysis of metaldns[.]com](https://cdn.umbrella.marketops.umbrella.com/wp-content/uploads/2018/02/25163814/6E12D72F-FB2A-4C43-BB12-F10C9708CB03-1024x228.png)
Thanks to our passive DNS data, we have domain names that we’ve seen resolving to the IP addresses of these suspicious nameservers. The following are a few interesting sights seen in this neighborhood while crawling through the domains found.
Lots of Open Space
There are plenty of open directories that lead to various phishing pages and kits.
![Path directory listing of administratore[.]com/email/emailamin/](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31124958/dir5.png)
![Index of tuasopdoc[.]com](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31124956/dir4.png)
![Index of docusigndatallc[.]com](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31124951/dir1.png)
Phishing Pond
If you continue down the walking path from the open space, you’ll make your way to the local phishing pond.

![Phising by banking impersonating https://www[.]alliancebank[.]com[.]my](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31124945/phish4-1024x697.png)


![Index of uoplo[.]com/mm/](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31202214/dir55-1024x820.png)

Have Some Crypto
By now, you’re probably getting tired and ready to take a break with some crypto. Here’s some of what the neighborhood has to offer for cryptocurrency.




Need a Boost?
There appears to be a large area devoted to Pharmaceutical fraud. Here are just a few.
![buylegitmeds[.]com phising site](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31124924/drugs3-1024x539.png)

![acelabs[.]pro phishing site](https://s3-us-west-1.amazonaws.com/umbrella-blog-uploads/wp-content/uploads/2018/01/31124919/drugs-1024x744.png)
The Local Hangout
End your day by meeting some of the locals.

It looks like you’re being invited to check out the local’s Bullet Proof Hosting (BPH) located at ns1[.]666webhost[.]com and ns2[.]666webhost[.]com.
At Cisco Umbrella, we see these neighborhoods of the Internet as hosting nothing but potential threats to our customers. We categorize them as Bulletproof Hosting, and have blocked all of the infrastructure highlighted above.
IPs:
193[.]109[.]68[.]43
193[.]109[.]68[.]58
5[.]39[.]219[.]119
101[.]99[.]72[.]47
111[.]90[.]144[.]253
141[.]105[.]67[.]101
111[.]90[.]144[.]251
BPH Nameservers:
ns1[.]steeldns[.]com
ns2[.]steeldns[.]com
ns1[.]metaldns[.]com
ns2[.]metaldns[.]com
ns1[.]666webhost[.]com
ns2[.]666webhost[.]com