With cryptocurrency reaching all-time highs (more than doubling since the start of the year), many people have looked to it as a form of investment. But as investors turn their attention to crypto, so do malicious actors. The market is set-up for attackers to cash in.
As the price of bitcoin (BTC) and other cryptocurrencies go high, we observe an increase in all types of attacks targeting crypto users. In contrast with common banking operations, cryptocurrency transactions are irreversible. When cryptocurrency is sent to a third party, the payment cannot be stopped or reversed. We covered a phishing scheme which left thousands of customers without their funds before and today we want to share what changes we observed within the past few months in the cryptocurrency threat landscape.
While phishing became less prevalent and less successful, we still track actors targeting cryptocurrency exchanges and trading platforms.
Some attempts are obvious and easy to spot, others are more sophisticated. These attacks use certificates which are either obtained by using hosting services such as Cloudflare, or obtained from an actual certificate authority.

Wildcard SSL certificate from CloudFlare used by phishing domain

SSL certificate from CA used by phishing domain
How attackers target Blockchain
Malicious actors which target Blockchain.com still utilize homograph attacks. These attacks are based on standards of the modern internet that allow the creation (and display in web browsers) of URLs with characters from various language sets (with non-ASCII letters). In the example below the real URL is login.xn--blockchin-c3a[.]com, but when rendered by the browser looks relatively legitimate. The issue is worse on mobile devices where the URL is not always displayed in full.

These fraudulent websites are distributed through a variety of methods including email, SMS text messages, social media, and search-engine advertisements. On average, such campaigns last for three to seven days and affect 20 to 40 users daily.
Cryptocurrency users are not the only ones in danger of their funds being stolen. Exchanges themselves can become victims of successful hacker attacks.
Uh-oh, what’s in your wallet?
With that in mind, more cryptocurrency owners turn towards cold storage options or wallets stored on their own computers. However, while you might think that you’ve made your crypto currency more secure, quite the opposite can happen. Malicious actors target wallets and their owners just as often as they target trading platforms or exchanges. Malicious wallets make their way into popular appstores and online by using fraudulent websites and trojanized binaries.
Here is an example of such an attack:

Malicious domain hosting trojanized wallet binaries
What makes things worse is that both the malicious binary and the legitimate one are detected as malicious by AV engines.

Malicious binary
Hash: 19388773fb5ac96ca0ea611bd10e71892c820effb0a70ee414faab03d5a2444b

Legitimate binary

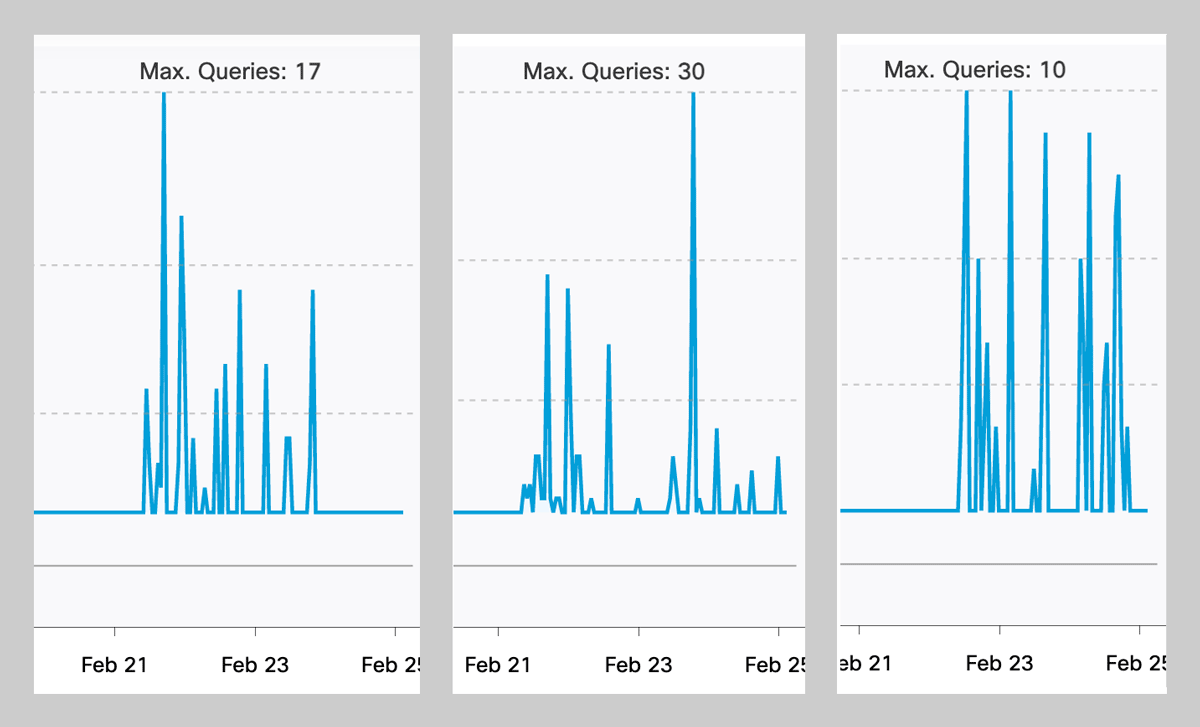
Attacker controlled server has consistent traffic peaking at 1.5k queries
If the user has such a wallet installed, all data including passphrase and private keys are exfiltrated to a server controlled by the attacker, who will transfer any available funds. Sometimes fraudulent wallets pose as an update to existing versions. In this case the user is transferred to an online webpage which asks to update or import previously generated wallets.

Malicious wallet asking for user secrets
However, the end goal of the attacker is the same – to recreate the wallet with user secrets and steal his funds. Other targeted hardware wallets include Ledger, Trezor and Mycelium.

Overall traffic to malicious cryptocurrency domains over last 28 days (excluding C&C traffic)
Tips to keeping your cryptocurrency safe
So if you’re a seasoned cryptoveteran or a new crypto enthusiast, you have to pay extreme caution while trading or storing your cryptocurrency. Here are a few key tips to keep your organization protected on every front:
- Be wary of common identifiers of phishing domains such as typos, broken links, and unusual contact information.
- Avoid clicking any links which come in the emails, sms, or social media.
- Be familiar with basic security such as:
- Two-factor authentication
- What suspicious files look like
- How to evaluate wallet apps or software.
The more widely a cryptocurrency is used, the more malicious actors they will attract.
Cisco Umbrella helps protect against malicious cryptomining
According to recent research using Cisco Umbrella global cloud architecture, 69% of Cisco Umbrella customers see cryptomining traffic on a daily basis. Cisco Umbrella resolves approximately 620 billion DNS requests daily — far more than any other security vendor. By analyzing and learning from internet activity patterns, Cisco Umbrella automatically uncovers current and emerging threats. Cisco Umbrella customers can detect, block, and protect against unwanted cryptomining in their environments, at no extra charge.
IOCs:
electrum-official[.]org
epayment-paxful[.]com
paxfuldeals[.]com
option-paxful[.]com
ppaxful[.]com
paxful-paid-offer[.]com
buybitcoinonline-paxful[.]com
legalpayment-paxful[.]com
gateway-paxful[.]com
ledger-live[.]co
ledgertoolkit[.]com
ledger-web[.]us
ledger[.]com[.]device[.]id[.]756728[.]app
wallet-login[.]app
ledger[.]com-authorization-login[.]app
ledger[.]com-verification-login[.]app
ledger[.]com-activity-login[.]app
ledger[.]com-login-secure[.]app
ledger[.]com-account-login[.]app
ledger[.]com-login-wallet[.]app
ledger[.]com[.]login-account[.]app
ledger[.]com[.]login-verification[.]app
ledger[.]com-login-activity[.]app
coinbase[.]com[.]connect[.]id73737[.]app
usa-ledger[.]com
ltc-electrum[.]org
coinbaseprologin-pro[.]com
electrumupdate[.]cc
electrumservice[.]com
electrum[.]download
electrum-bch[.]com
exodus-login[‘.]com
logins-kraken-in[‘.]com
kraken-app[.]com
kraken-accounts-fr[.]com
kraken-balances-us[.]com
exoduswalletweb[.]live
exodusmainwallets[.]live
exoduswalletsio[.]live
com-account-login[.]app
com-activity-login[.]app
com-authorization-login[.]app
com-login-account[.]app
com-login-activity[.]app
com-login-secure[.]app
com-login-wallet[.]app
com-verification-login[.]app
poloniex-asset[.]com
kraken-logins-fi[.]com
xn--blockchin-c3a[.]com
Xn–coinbse-9wa[.]com
