A cloud access security broker (CASB) is a cybersecurity solution that serves as an intermediary between users and the cloud services that they rely on for day-to-day activities. It allows security or IT teams to enforce policies that govern users’ access to and use of cloud services. This can prevent data loss, ensure regulatory compliance, and reduce the risk of cyberattacks on the company network.
Given the prevalence of cloud-delivered services and the security benefits provided by a CASB, it should come as little surprise that Gartner lists cloud access security brokers as essential components in any Secure Access Service Edge (SASE) or Security Service Edge (SSE) solution. But for enterprises just now embarking on their SASE journey, evaluating the CASB security functionality offered by vendors can feel a bit daunting. What should one look for in a cloud access security broker? How can IT or security teams make the most of an integrated CASB?
We set out to answer the second question in our ebook Secure Shadow IT, which digs into practical ways that teams can use cloud app discovery functionality to mitigate the risk of unsanctioned cloud services use. But in this blog post, we’re focusing on the first question. We’ll unpack what a CASB is and how to choose a solution that will help you on your SASE journey.
What Does a Cloud Access Security Broker Do?

Most modern enterprises rely on cloud services for day-to-day operations. These services, and the apps associated with them, allow on-premises, remote, and roaming employees to connect to the software, infrastructure, platforms, and data they need to accomplish even the most basic of tasks. Because of this, having a designated cybersecurity solution that mitigates risks caused by cloud usage is a must.
You can think of a CASB as the security station in front of an office building. Every time users engage with cloud-based applications – every time someone enters or exits our metaphorical office building – a CASB can inspect the traffic and:
- Identify the specific cloud service being used, regardless of whether it has or hasn’t been sanctioned by the IT team
- Determine whether the data being sent from the company network to the cloud application is permitted by existing security policies
- Prevent unauthorized app usage or data transfer
- Flag any files containing malicious programs that could lead to a security incident
The security policies created and implemented using a CASB can be either broad or granular. For example, security teams can prevent the usage of risky cloud applications or apps that might not be compliant with industry regulations. U.S. schools looking to maintain CIPA compliance could block apps related to adult content. Medical facilities looking to maintain HIPAA compliance could block cloud data storage apps with a history of compromises.
But a cloud access security broker doesn’t just block apps. It can also control how employees use them. For example, the policies created in a CASB can govern whether employees can use file sharing apps to send files to users outside of the company. Or, these policies can allow employees to view files in certain apps, but not download or upload files from them. Nuanced policies allow employees to engage with popular apps used by individuals outside of your organization without running a heightened risk of data loss.
Because of this functionality – and the prevalence of cloud services in most modern enterprises – a cloud access security broker is a crucial tool for threat protection and data loss prevention. The enhanced app visibility provided by a CASB can also help businesses optimize cloud service usage, as it shines a light on overlapping SaaS, PaaS, and IaaS subscriptions.
How to Choose a CASB Security Solution That Fits Into Gartner’s SASE Model
Remember, the goal of Gartner’s SASE model is to provide comprehensive functionality with a simplified interface. While most enterprises can’t upgrade to that Jetsons-esque, converged and cloud-delivered infrastructure overnight, thinking through your CASB security solution in light of your SASE journey is still worthwhile. That’s because a cloud access security broker features prominently in Gartner’s SASE model, as well as their newer Security Service Edge (SSE) concept that exclusively focuses the requirements for an integrated, cloud-delivered cybersecurity service.
When the time comes to invest in a new cloud access security broker, you’ll get the biggest return on your investment by partnering with a SASE vendor that:
Integrates CASB Functionality With Other Cybersecurity Solutions
An integrated cloud access security broker will be designed to easily share logs with other cybersecurity solutions in your stack, like a secure web gateway (SWG) or data loss protection (DLP) tool. This integration and log sharing gives security teams a more comprehensive view of what’s happening on a network regardless of whether employees are accessing the Internet directly or using cloud-based applications.
It also makes it easier for security teams to design and implement effective policies. Your team won’t have to move data to or from a siloed CASB to make it actionable. And instead of trying to create coordinated policies across siloed solutions – which is often frustrating at best and can lead to gaps in coverage at worst – your team will be able to create policies that utilize different security functionalities from a single dashboard.
Provides a Simple and Scalable Cybersecurity Solution
If your organization is like most, odds are that cloud app usage on your network fluctuates depending on current remote work policies or technology developments. As you cycle cloud services out of your organization’s workflow or roll out cloud services across large numbers of users, you need a cloud access security broker capable of ranking and interfacing with a wide variety of cloud apps.
You also need your vendor to be able to provide consistent and reliable service as your business grows. This is where partnering with a SASE vendor for your CASB security needs comes in handy – these solutions are designed with scalability in mind, so adding more users to tenant-based security policies shouldn’t meaningfully interrupt quality of service.
How Does the CASB Functionality of Cisco Umbrella Fit Into Your SASE Journey?
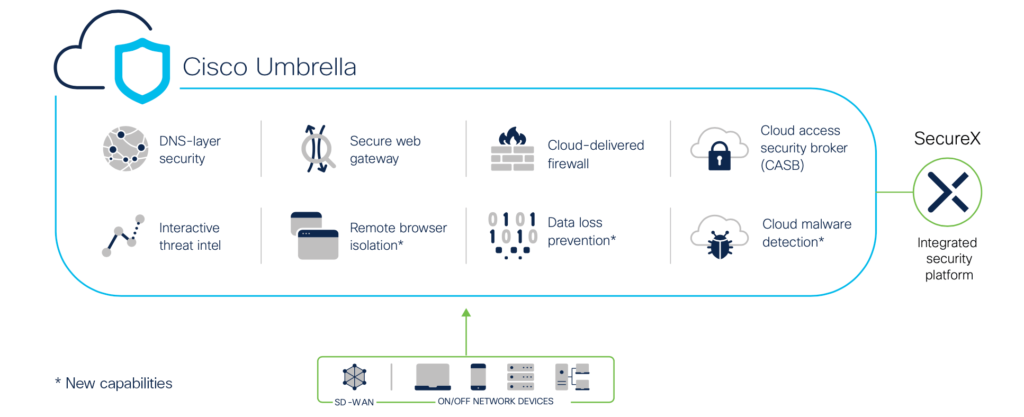
Designed to be an all-in-one, cloud-delivered security solution, Cisco Umbrella offers users a simple, efficient, and effective cybersecurity experience. Because of this, the CASB functionality included in the Cisco Umbrella SIG Essentials and SIG Advantage packages integrates seamlessly with the additional security functionality required in a SASE or SSE solution.
The CASB security functionality included in Cisco Umbrella also empowers security or IT teams to:
- Perform cloud app discovery at scale, cutting down on shadow IT across an organization
- Create granular security policies that manage cloud app usage via tenant controls or activity restriction
- Prevent data loss with in-band DLP functionality – available to all Cisco Umbrella SIG Essentials and SIG Advantage customers
With more than 250,000 cloud applications discovered, more than one billion files monitored daily, and 10 million users under management, the cloud access security broker functionality of Cisco Umbrella boasts an exceptional track record. Because of this, enterprises starting their SASE journey by upgrading their cybersecurity stack won’t find a smoother onramp.
Are You Ready to See What a Cloud Access Security Broker Is Capable Of?
Download our ebook Secure Shadow IT to dig into how your team can use the CASB security functionality of Cisco Umbrella to gain app visibility, analyze risks, and optimize or secure app usage.
Or, if you’re ready to see Cisco Umbrella in action, request a free demo today!
1 Gartner. “Cloud Access Security Brokers (CASBs).”
