Batman and Robin.
Peanut butter and jelly.
And now, Meraki and Umbrella.
All great duos, all better together.
We’re excited to announce a new, simple, and powerful integration between Cisco Meraki MR access points and Cisco Umbrella. This integration is the absolute easiest and fastest way to deploy Umbrella across a wireless network. Effortlessly protect all your users and devices on your Meraki wireless networks, with just a few clicks. The integration allows networking and security administrators to conveniently enable Umbrella policies directly within the Meraki dashboard. And it enables administrators to create granular policies on a per-SSID basis or by using Meraki group policies.
How does it work?
- Link Accounts

In the Umbrella dashboard, you’ll copy your API key and Secret and input into the Meraki dashboard. The API Key and Secret are used to identify your Umbrella account within Meraki.
- Select Umbrella policies
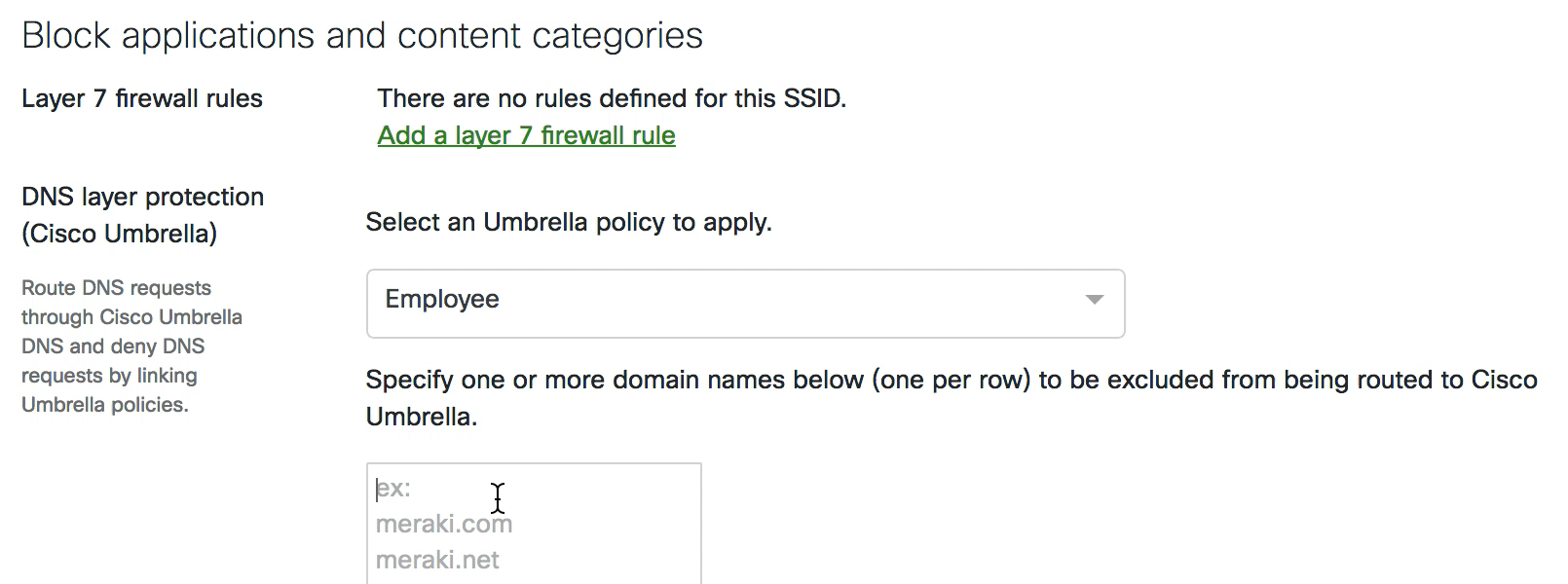
In the Meraki dashboard, select which Umbrella policy you’d like to apply to the SSID. For example, you could create separate Employee and Guest policies in Umbrella and enforce those policies across your Employee and Guest SSIDs, respectively. You can also use Meraki group policies, providing additional granularity.
- That’s it. Once you select an Umbrella policy, all users and devices on your Meraki network are protected.
No changing DNS — it all happens automagically. 
How can I take advantage of the integration?
There is no additional cost or charge for existing Meraki or Umbrella customers that want to take advantage of this integration.
- Meraki: At this time, customers can access the integration by contacting Meraki support. Read the Meraki documentation.
- Umbrella: Visit “API Keys” located in the Admin section of the Umbrella dashboard to get started. Read the Umbrella documentation.
If you’re not currently a Meraki or Umbrella customer, you can test out both products for free.
There are three ways to try Meraki: you can request free trial gear, get a free access point by attending a webinar, or view an instant demo. Visit this page to get started. To try Umbrella: visit signup.umbrella.com and sign up for a free 14 day trial. No credit card or phone call required.
Some technical tidbits
| Integration feature | Why it matters |
| Appends EDNS (Device ID and Client IP) to the DNS packet. | Enables Umbrella to enforce the right policies for the right devices (Device ID) and provides visibility in the Umbrella dashboard (Client IP). |
| Supports split DNS to exclude internal DNS requests from being sent to Umbrella resolvers | Allows users to reach your network’s local resources (computers, servers, printers, etc.) on internally-hosted domains that rely on local DNS servers. |
| Supports DNSCrypt proxy to encrypt the DNS traffic | Secures DNS traffic from eavesdropping and man-in-the-middle attacks. |
The products behind the integration
Meraki MR
Cisco Umbrella