Emotet is a trojan that steals financial information, AKA, “Banking Malware”. Trojans give cybercriminals a backdoor to systems, making it possible to spy on confidential information like banking credentials and to exfiltrate data. In order to get a trojan onto a system, an attacker will want to disguise it as something else.
Once the Christmas holiday season rolled around, the malicious actors behind Emotet started sending out some unwanted gifts to email inboxes. The emails appear to be wishing you a Merry Christmas and sending you a holiday gift card, or an E-card greeting. They include a link that downloads a malicious word document and if macros execute, the Emotet trojan is downloaded to the system. The link leads to a compromised website. The URIs in the links have been similar to “Your-Holiday-Gift-Card”. The downloaded document will be named something similar.
We’ve seen the malicious actors continue to use this tactic since Christmas, and on into this week.
The various URIs we have observed:
- /Your-Holidays-eCard
- /Gift-Card-for-you
- /eGift-Card
- /Happy-Holidays-Card
- /Your-Gift-Card
- /Christmas-eCard
- /Your-Christmas-Gift-Card
- /Holidays-eCard
- /Gift-Card
- /Your-Card
- /eCard
Re-Gifting
Throughout 2017 Emotet relied on spam messages that included attached malicious word documents of fake invoices from various companies and sometimes “voicemail” attachments. It then evolved to contain links in the message body that lead to the download of the word document.
The invoice tactic contains URIs on compromised sites using words similar to:
- /Invoice
- /Overdue-payment
- /Final-Account
- /Invoices-attached
- /Invoice-01075710
This URI pattern works to look legitimate to individuals that deal with accounts payable, shipping, finance, etc. Someone that deals with many invoice requests in a day may not find the type of attachment or download out of the ordinary.
Unwrapping the Gift
Document download:
- http://www[.]jackbenimbleonline[.]com/Gift-Card-for-you
Hash:
- 6e4a276dd2d745f57faa6e18ba90e255836ef4976c65cdfd831412b8ae4ab91c
C2:
- 178[.]32[.]255[.]132
The macro included in the word doc executes a powershell script that downloads the payload. The emotet banking trojan is downloaded and often times additional malware.
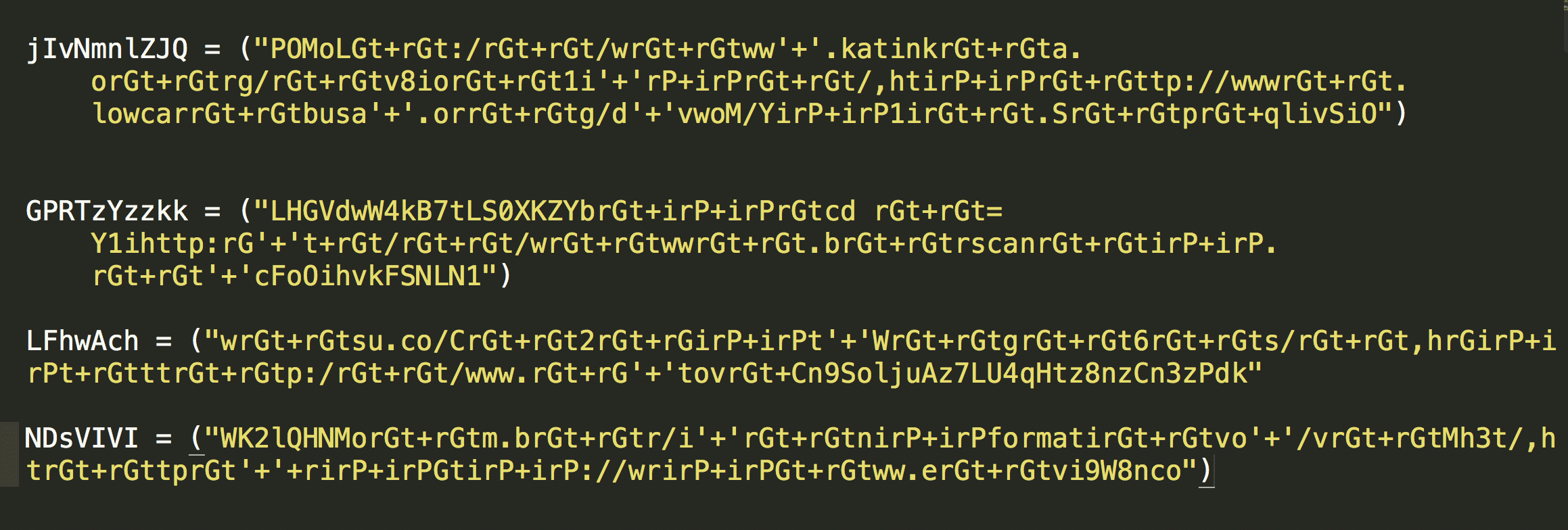
The powershell script is obfuscated, but with some effort we can find the possible URLs that will be contacted to get the payload.


The Reason for the Season
Many of the compromised sites were running outdated WordPress versions 3.5 through 4.7 which has multiple vulnerabilities where attackers can inject malicious script and html, compromising the site.
A few of these compromised sites appeared to have tried to clean up and failed. One of the compromised sites seems to have performed a WordPress upgrade without removing the infected URLS and a SEO spam infection, showing a lingering security problem.

The latest URLs that we have seen hosting the malicious doc files:
- http://jackbenimbleonline[.]com/Gift-Card-for-you
- http://bezbarier[.]wasko[.]pl/Your-Holidays-eCard
- http://raymain[.]co[.]uk/Your-eCard/
- http://www[.].sodocimeb.com[.]do/Your-Christmas-Card/
- http://www[.]forenadebolag[.]se/Your-Holidays-eCard
- http://www[.]join[.]us/Your-Holidays-eCard
- http://www[.]sdkhunter[.]com/Gift-Card-for-you
- http://sacrafamigliatrento[.]it/Gift-Card-for-you
- http://m-onefamily[.]com/components/eGift-Card
- http://usammm[.]org/eGift-Card
- http://www[.]twitchsleep[.]net/Happy-Holidays-Card
- http://www[.]queenstreetlaundry[.]com/Your-Gift-Card
- http://vmediaacademy[.]com/Christmas-eCard
- http://circadianpulse[.]com/Your-Christmas-Gift-Card
- http://hotelpetresort[.]com/Holidays-eCard
- http://wallhult[.]se/Holidays-eCard
- http://ortospinecenter[.]com/Gift-Card
- http://qttctc.edu[.]vn/Gift-Card
- http://www[.]simonedipasquale[.]com/Gift-Card
Associated Hashes:
6e4a276dd2d745f57faa6e18ba90e255836ef4976c65cdfd831412b8ae4ab91c
314534b97bbe3cf2d71e95234c1fe8e5079e8fc3792d237c62d713d83c2bf50e
Ce0c66e61a98e7517e3c496e077ed07783d26a7994ec39010e258c4fd7d01ea9
B051137a784c2f67be25b55b4ec61362720bb12a909c99da6b967922faa2646b
a77e40b03e814c6f554929a939839416d80f73228a123ab953be37a1f25780b5
D038049d22c876e826cf41e0f69089d9a01654f48790c53202cbfa98bcf8c6eb
87dc2f7b36c4423f641516068c94feb3c9a634fbaa9196244cbf03bed8f2c85a
43e7bcef39f88ca7d3b9b67d09f9264c4946e0e12a337c23e043bb8e9f634c2e
6e2460dab20fcca216798641dfa821e73b5bccf510df487839f542a198740778
F9cf6788755dc5f82017e62b08f8f36eaf92806de4c89110207a13da27d7529f
C412ad121682d33210402955ad330fbd182c5c57155bab2db659c7557d4a417b
A8c75f9b1e601c4c77b67ddd1bdb28bf9164c4f507b9530fa31861f2c72fb2d7
D007c2ec4483fcd4dbf67233956b194d3a3a46426f700282ea7b01785a10fc50
Dcab1d68887140ae7597993d166babeb0792f12ef9388e5cab89e9f4ee4b329f
Fba9ba4112dacc745d951a00f20c1e967bf78cbb318e947d695f08c42fb588c2
C2 servers observed in the samples:
91[.]121[.]45[.]118
49[.]212[.]135[.]76
195[.]154[.]58[.]200
65[.]44[.]220[.]49
178[.]32[.]255[.]132
212[.]5[.]159[.]61
Cisco Umbrella will continue investigating these “gifts” in order to block new malicious infrastructure used by cyber criminals as they continually change their tactics.
Enforce deeper security and control with a Secure Web Gateway
Get more control, transparency, and protection from trojans like Emotet with Cisco Umbrella’s Secure Web Gateway (SWG). It provides cloud native, full proxy capabilities to improve performance and reduce risk by efficiently logging, inspecting, and controlling web traffic. Security doesn’t have to be complicated.
