So, you think you already know the good, the bad, and the ugly about cybersecurity threats, such as malware and phishing, that small and medium-sized businesses (SMBs) are facing? You may be surprised.
People often make a number of assumptions that can easily miss the mark. There is a tendency to fall into the trap of thinking that smaller means less concerned or less of a threat. But as the Cisco 2020 Cybersecurity Report, Big Security in a Small Business World, demonstrated, SMBs actually face many of the same challenges as their larger kin.
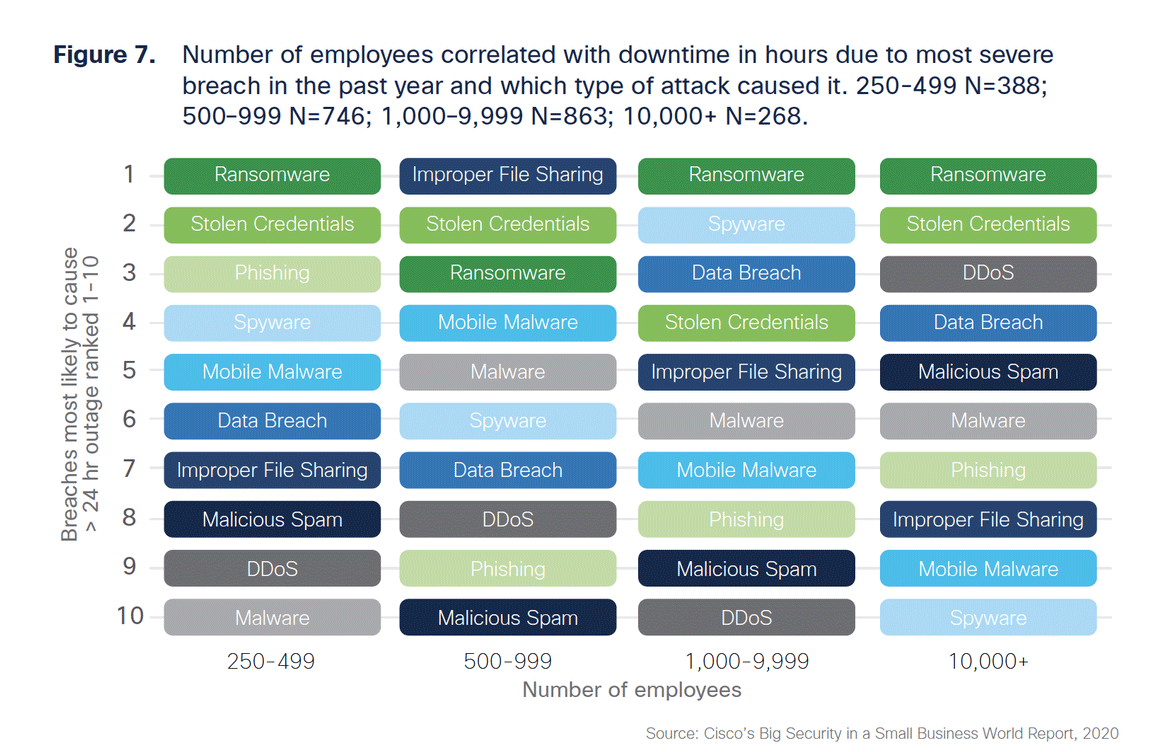
That report found that there weren’t a lot of differences in the types of threats that SMBs face from those that threaten larger organizations. Ransomware and stolen credentials are big problems for pretty much everyone. However, phishing and mobile malware do show up as bigger issues for smaller organizations. This, perhaps, reflects a greater reliance on people to thwart social engineering in SMBs and a greater reliance on multiple devices for endpoint IT access.
Similarly, Cisco Umbrella’s late 2020 threat landscape report, The modern cybersecurity landscape: Scaling for threats in motion, found a large jump in phishing, primarily driven by pandemic-related themes, nearly doubling from 46 to 83 percent.
The data that delivers that insight comes from the Cisco Umbrella global cloud architecture, which processes more than 350 billion DNS requests per day, representing 100 million active users and more than 30,000 enterprise customers from 190+ countries. Using that data, the threat landscape study identified four major trends.
- Trojans and droppers are getting a second life as new forms of malware delivery.
- Orchestrated, multi-staged, evasive attacks are becoming the norm.
- Cryptomining is opening the door to other types of cyberthreats.
- Attackers are taking advantage of pandemic-related content to propagate more phishing attacks.
Trojans like Emotet and Gozi, which have been around for years, are being used and re-used to evade traditional anti-virus defenses and deliver new malware. This is typically part of an orchestrated, multi-stage attack incident, which is becoming more prevalent on the threat landscape.
Cryptomining, though it is often viewed as “no harm, no foul,” actually opens the door to tremendous risk and can be an outright threat on its own if the software is not browser-based.
The rise in pandemic-related themes has put a spotlight on the phishing that attackers will use to exploit fear-based openings into your operating environment. Fear-based exploits are always popular, as fear clouds judgement and opens the door to more risky behaviors.
SMBs, while subject to the same cyber threat drivers as larger organizations, may find that their people play a more significant role in thwarting such malicious social engineering. While greater scale demands automation to reduce risk in larger organizations, humans stopping humans takes center stage for deterrence among SMBs.
All of us, regardless of size, are grappling with making the best use of limited resources against a constantly evolving, ever-innovating adversary. While SMBs may not have the big budgets of the larger organizations, the prominence of individual humans and small teams provides unmatched clarity and focus in the battle of human wits to thwart adversaries with malicious intent.

