Last year threw a lot at cybersecurity teams, from the emergence of several high-profile cyberattacks to the revelation of widespread vulnerabilities. As we all move into 2022, odds are your team is re-thinking your cybersecurity strategy to help make your organization more resilient and flexible. This should involve an evaluation of your cybersecurity solutions, as they impact the implementation and effectiveness of any strategies your team creates.
In our ebook 7 ways to strengthen your security in 2022 and beyond, we discuss the different ways you can amplify and extend your cybersecurity stack this year using Cisco Umbrella. But if you’re looking for some tips to get you started, here are three things to keep in mind as you plot out your cybersecurity strategy:
1. Make Sure Your Cybersecurity Solutions Don’t Impact Network Speeds
The use of internet resources and cloud services was on the rise before the COVID-19 pandemic. Now that employees have spread out – collaborating with coworkers and performing business-critical tasks from anywhere they have internet access – cloud-based tools have become more critical than ever.
This means that an effective cybersecurity strategy needs to balance the implementation of strong protections against the need for minimal latency on the company network. From a business perspective, cyber safety can’t come at the expense of speed.
In order to maintain this balance, take a look at your cybersecurity solutions and evaluate the following:
- Routing Algorithms – Frequently, having fast and secure internet access comes down to a cybersecurity vendor’s data center network and routing algorithms. Make sure your cybersecurity solutions come backed by a robust global data center network and transparent routing protocols with automated failover to the fastest available servers. This minimizes latency, regardless of where users on your network are located.
- Peering Relationships – Peering relationships allow cybersecurity vendors to minimize latency without compromising on security. As you reevaluate your cybersecurity strategy in the coming year, make sure your vendors have peering relationships with large cloud service providers your organization relies on. This allows employees to easily access the tools they need without introducing added latency.
Keeping network speeds in mind while you refine your cybersecurity strategy for the upcoming year can improve employee satisfaction, affect executive buy-in, and have an impact on your organization’s bottom line.
2. Strengthen Cybersecurity Infrastructure to Reduce Disruptions
Last year, we all experienced more than our fair share of network disruptions, outages, and downtime. Several of these events were impactful enough to make it into the news cycle. And while an outage isn’t the same thing as a cyberattack, your cybersecurity strategy should include finding solutions that are designed to reduce downtime instead of causing it.
Take some time to review the track record of your vendors. For example, do they have a proven record of resiliency and uptime? Better yet, can they handle infrastructure disruptions without passing those disruptions onto your users? For example, the unique DNS logging features included in Cisco Umbrella DNS-layer security can be used during certain events – like the 2021 Akamai outage – to keep users connected to business-critical cloud tools despite provider outages.
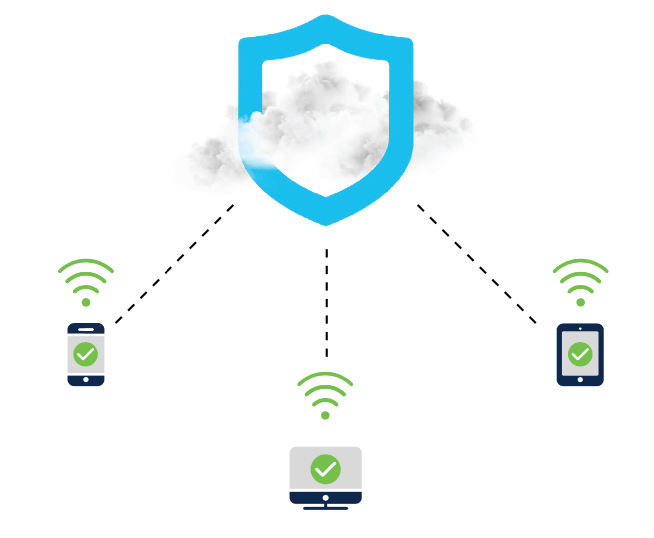
3. Make Sure Your Cybersecurity Strategy Includes Guest WiFi Considerations
Between the move to a hybrid work model and the gradual reopening of public spaces, odds are you’ll find more employees and clients using your guest WiFi in the coming year. So, it’s essential to make sure that both your private and guest WiFi networks have the speed users desire and the protection you need.
Does your suite of cybersecurity solutions provide your team with the ability to filter content and enforce security protocols over your guest WiFi network? Does your security stack allow you to maintain a single IP address for your entire enterprise, streamlining the management of guest WiFi security policies? Finally, can your cybersecurity solutions handle the uptick in user traffic that guest WiFi causes without increasing latency? If the answer to any of these questions is “no,” it may be time to think about adjusting your security stack.
Looking for More Ways to Strengthen Your Cybersecurity Strategy?
Download our ebook 7 ways to strengthen your security in 2022 and beyond today to discover more ways that you can use Cisco Umbrella to strengthen your cybersecurity strategy this year.